
A Data-Driven Guide to Modern Office Security
When you think about security at the office, it's easy to picture locked doors and alarm systems. But that's a dangerously outdated view. Real security today is a unified system protecting your physical space, digital data, and people. A single weak link can compromise the entire operation.
Rethinking Security in the Modern Office
The old paper sign-in book at the front desk is a relic. Today's offices are dynamic hubs with employees, clients, contractors, and couriers constantly moving through. Unmanaged, every entry point is a potential vulnerability.
The lines between physical and digital security are gone. A contractor plugging an infected USB drive into your network can trigger a massive data breach. A single phishing email can lead to stolen credentials, giving an attacker physical access to your building. It’s no surprise that 74% of all breaches involve the human element. Your security is only as strong as your least prepared employee.
The Urgency of an Integrated Approach
Treating physical and digital security separately creates dangerous gaps for attackers to exploit. You need an integrated strategy where all your security tools work together as a unified defense.
A modern visitor management system is the cornerstone of this approach, offering immediate benefits by providing a vital layer of control and visibility at your front door:
- Gain Total Visibility: A real-time, accurate log of everyone on-site isn't just a convenience; it's essential for safety, compliance, and incident response.
- Boost Employee Confidence: When visitors are properly screened and hosts receive instant notifications, your team can focus on their work, knowing their environment is secure.
- Ensure Business Continuity: By preventing disruptions from theft, vandalism, or unauthorized access, you protect your assets and maintain smooth operations.
A proactive security posture is built on visibility and control. Knowing who is in your building, why they are there, and that their presence is authorized is the first and most critical step in protecting your entire organization.
Many companies are now adopting a "zero trust" model to protect digital assets—a mindset that requires verification at every step. You can learn more by understanding zero trust security and applying its principles to your physical space.
Ultimately, a robust security plan benefits everyone. It streamlines the visitor experience, empowers employees with instant updates, and gives leaders the data needed for smarter decisions. Learn how to setup security notifications to keep your team informed and prepared.
Navigating Digital Threats in the Workplace

While a locked door provides a sense of safety, today's biggest threats often bypass it entirely, exploiting digital backdoors. Understanding these modern risks is the first step toward building a defense that actually works.
Forget simple viruses; modern cyberattacks are sophisticated and organized. From convincing phishing emails designed to steal credentials to ransomware that can halt your entire operation, the goal is clear: access your data and your money.
The Modern Cyberattack Landscape
Cybercrime is now a professional industry. Ransomware-as-a-Service (RaaS) models allow criminals with minimal technical skill to "rent" powerful attack tools, leading to a massive surge in attacks against businesses of all sizes.
The consequences are escalating. In fact, a staggering 93% of organizations view cyber risk as a top business concern. It's a clear sign that digital security is no longer just an IT problem—it's a core business function that demands attention from the front desk to the boardroom.
How Digital and Physical Security Intersect
The most dangerous blind spot for most businesses is the gap between digital and physical security. A state-of-the-art firewall is useless if an unauthorized person can simply walk into your server room.
Consider these common scenarios where this gap is exploited:
- The Unvetted Contractor: A technician arrives for a repair. Without a proper check-in, they could plug a compromised device into your network, bypassing your digital defenses in seconds.
- The Malicious USB Drop: An attacker leaves a USB drive labeled "Q3 Financials" in the parking lot. An employee finds it, plugs it in out of curiosity, and unleashes malware.
- The Tailgating Threat: An unauthorized person follows an employee through a secure door. Once inside, they have physical access to cause significant damage.
A single physical breach can nullify your entire cybersecurity investment. When an attacker gains physical access to your network, they can bypass layers of digital protection that were designed to stop external threats.
Strengthening your office entry points is a critical part of your digital defense. A modern visitor management system provides the benefit of a clear, auditable record of every person who enters, ensuring every visitor is identified and authorized before they get near sensitive equipment.
As you navigate these risks, it's also worth learning about specific attack vectors, like web cache deception techniques. The only way to truly protect your business is with an integrated strategy that combines strong digital protocols with equally strong physical access controls.
Strengthening Your Physical Security Defenses

While digital threats dominate headlines, the physical security of your office remains the bedrock of your protection strategy. It's your first line of defense, yet it's often filled with overlooked vulnerabilities that are exploited daily.
Think of your office lobby as the main gate. If left unsecured, it becomes your biggest liability. Seemingly small oversights here can escalate into major incidents, from stolen equipment to catastrophic data breaches.
The Dangers Hiding in Plain Sight
The most common physical security gaps are the ones we tend to dismiss. A shocking 75% of employees admit they would hold a secure door open for a stranger. This single act of politeness, known as tailgating, completely negates even the most advanced lock systems.
Other frequent risks include:
- Unmonitored Visitors: Guests or contractors wandering unescorted can easily access sensitive areas or view confidential information on screens.
- Anonymous Entry: Without a robust check-in process, you have no verifiable record of who is in your building at any given time, making investigations nearly impossible.
- Outdated Logbooks: Paper sign-in sheets are a security nightmare. They are easily forged, lost, or read by other visitors, creating significant privacy risks.
These vulnerabilities aren't just about preventing theft. An unauthorized person gaining physical access could plug a malicious device into your network, triggering a ransomware attack. This is a classic example of how a physical security failure leads directly to a digital disaster.
Transforming Your Lobby into a Secure Hub
A modern visitor management system turns a vulnerable entryway into a secure and professional hub. The benefit isn't just about logging names; it's about creating an environment of proactive security from the moment someone arrives.
By automating the check-in process, you immediately elevate your office's security. This ensures every individual—from a high-profile client to a one-time contractor—is properly identified, verified, and accounted for. You gain the peace of mind that comes from knowing exactly who is on-site and why they are there.
This enhanced control makes employees feel safer, allowing them to work with confidence. It also provides a seamless and professional experience for legitimate guests, reinforcing your company's commitment to security and organization.
The real win with a robust visitor management system is certainty. You're replacing assumptions and guesswork with a clear, verifiable record, making sure only the right people get into your space.
Enhancing Safety and Operational Awareness
Knowing who is in your building is also critical for crisis management. During an emergency, an accurate, real-time list of all personnel and visitors is invaluable for a safe evacuation. You can learn more by reviewing comprehensive emergency evacuation procedures for the workplace.
A visitor management system provides this vital information instantly, allowing you to account for everyone and give first responders the data they need. It shifts your security from a reactive stance to a proactive one, safeguarding both your people and your assets. By securing your front door intelligently, you strengthen your entire organization.
The Human Element in Office Security
Your technology and physical barriers are crucial, but your people are the ultimate gatekeepers. While employees are your greatest asset, they are also the primary target for attackers. This isn't a reflection of their loyalty; it's a reflection of how modern threats are designed.
Attackers often bypass complex digital defenses by focusing on a much softer target: human psychology. They use social engineering—manipulation designed to trick people into divulging confidential information or taking actions they shouldn’t.
Why Even the Best Employees Can Be Tricked
Social engineering works because it exploits basic human tendencies like trust, urgency, and a desire to be helpful. A fraudulent email that appears to be from a senior manager with an "urgent request" can easily pressure an employee into a mistake. The data is clear: social engineering is a factor in 98% of cyberattacks.
This statistic makes it undeniable: even with the best technology, your security can fail if your team isn’t prepared.
The chart below visualizes some key security trends over the past few years, including breach data and detection times.
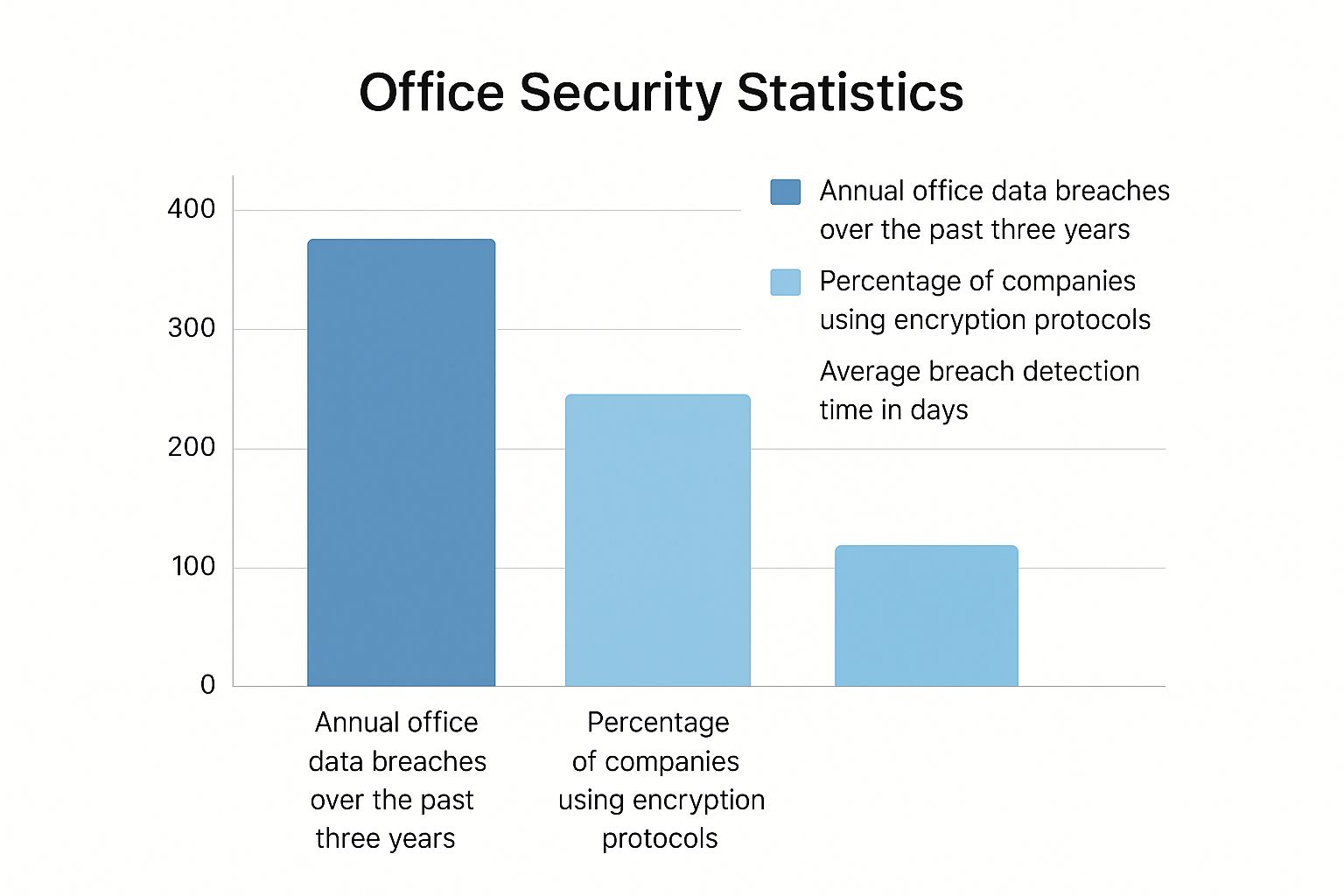
As you can see, the time it takes to detect and contain a breach remains a major challenge, highlighting the need for faster, more automated ways to identify threats.
Building a Security-First Culture
Strengthening your human defenses means building a security-first culture where awareness is second nature. This requires moving beyond a single annual training session to continuous, engaging education that empowers your team.
Effective training gives employees the confidence to question suspicious requests and the knowledge to spot red flags instinctively. A well-trained team becomes an active part of your defense, not just a potential vulnerability.
Here's how training and technology work together to mitigate common human-related risks:
Human Element Risks vs Mitigation Benefits
| Common Risk | Potential Impact | Mitigation Strategy Benefit |
|---|---|---|
| Social Engineering | Unauthorized access, data theft, financial loss. | Training helps staff recognize phishing. Technology (like a VMS) automates ID verification, reducing reliance on manual checks that can be manipulated. |
| Tailgating | An unauthorized person follows an employee into a secure area. | Training fosters a culture of vigilance. A VMS ensures all visitors have a verified reason to be there, with a designated host. |
| Simple Human Error | Accidentally sharing sensitive info or leaving a secure door propped open. | Awareness training reduces mistakes. A VMS provides a digital audit trail, logging who is on-site and when for effective incident reviews. |
| Insider Threats | A disgruntled or negligent employee intentionally misuses their access. | Access controls limit individual permissions. A VMS tracks visitor movements, making it harder for unauthorized collaborations to occur. |
By combining smart tools with a well-informed team, you create multiple layers of defense that are much harder to penetrate. A modern visitor management system plays a powerful supporting role in this culture by automating critical verification processes.
When visitor check-ins, ID verifications, and host notifications are handled automatically, it frees up your employees to focus on their core responsibilities with confidence. They are no longer burdened with the complex task of manually vetting every person who walks through the door.
This automation not only tightens security but also helps your team manage unexpected arrivals more effectively. For more strategies, check out our guide on how to deal with unscheduled visitors to the office. Empowering your team with smart tools creates a safer, more welcoming environment for everyone.
Using Technology for Smarter Office Security
Relying on outdated security methods is like navigating with a paper map in the age of GPS—it just can't keep up. Technology is the engine of a modern security at office strategy, creating a responsive ecosystem that can react to threats faster than humanly possible.
Instead of just recording events, modern security systems actively search for anomalies. AI-powered analytics can detect unusual patterns—like an access attempt in a restricted area at 3 a.m.—and flag them instantly. This benefit turns your security from a passive observer into an active guardian, slashing response times and minimizing potential damage.
The goal is to build a proactive security posture that anticipates risks rather than just cleaning up after an incident. This is where a unified defense, with a visitor management system at its core, makes all the difference.
The Visitor Management System as a Central Hub
Think of a modern visitor management system (VMS) as the central nervous system of your office security. It connects and coordinates your other security tools, creating a single, powerful network that delivers real-world benefits.
This integration creates a seamless, automated security workflow:
- Access Control Integration: When a visitor checks in, the system can automatically grant temporary access only to the specific areas they need, revoking it the moment they sign out.
- Camera System Synergy: If a security alert is triggered, the VMS can instruct the nearest camera to focus on the entryway and notify security personnel.
- Instant Communication: The system can send automatic alerts via email, SMS, or Microsoft Teams to notify an employee of their guest's arrival or alert security to an issue.
By acting as a central hub, a visitor management system ensures that all your security components are working together. This unified approach eliminates dangerous gaps and creates a cohesive defense that is far more effective than individual, disconnected tools.
For organizations that also need to secure their software development, digging into DevOps security best practices can offer great insights for protecting digital assets from the ground up.
Harnessing AI for Proactive Threat Detection
Artificial intelligence provides a serious security advantage. Its real power lies in its ability to analyze vast amounts of data and identify subtle threats in real time that a human would miss.
An AI can learn the normal rhythm of your office—who comes and goes, and when. It can then spot anomalies, like an unfamiliar face tailgating an employee, and trigger an immediate alert. This creates a proactive defense that is always hunting for threats.
However, implementation is key. While AI adoption can speed up threat detection, poor governance can increase risk. A recent report found that organizations using AI and automation extensively in their security frameworks identified and contained breaches 74 days faster than those that didn't. This highlights the clear operational and financial benefits of a well-managed, AI-driven strategy.
By integrating smart technologies, your office becomes an intelligent, secure environment. A solid visitor management system for offices acts as the foundation, providing the control and visibility needed to manage access. This allows other advanced tools, like AI-powered cameras, to operate from a position of strength, making your entire security ecosystem both smart and resilient.
Common Questions About Office Security
Navigating office security brings up many questions, especially as threats and technology evolve. Here are concise answers to the most common concerns about keeping the workplace safe.
Where Should We Start With a Limited Budget?
With a limited budget, start with a simple risk assessment to identify your biggest physical and digital weak spots. This allows you to focus spending where it will have the greatest impact.
Often, the most cost-effective investment is in your people. Regular, engaging security training turns every employee into a frontline defender against threats like phishing and social engineering. Another high-impact, foundational step is implementing a modern visitor management system. It provides the immediate benefit of controlling and tracking everyone who enters your office, significantly boosting physical security without a massive budget.
How Can We Improve Security Without an Unwelcoming Atmosphere?
The key is to use security measures that are seamless and professional, not intimidating. A modern visitor management system is a perfect example. It replaces a clunky paper logbook with a sleek, digital check-in that is quick and efficient for guests.
This approach offers the benefit of robust security—verifying identities and tracking visitors—while presenting a welcoming, modern experience.
The best security is the kind people barely notice. The aim is to build a safe environment that actually makes the day better for employees and guests, not one that gets in their way.
Technology handles the heavy lifting of security in the background, allowing your team to focus on creating a positive, collaborative atmosphere.
What Is the Single Biggest Security Mistake?
The biggest mistake is treating security in isolated silos. When physical security, cybersecurity, and employee training are managed by separate teams that don't communicate, you create exploitable gaps.
Attackers don't see separate categories; they see one target. A physical breach, like an unvetted contractor entering a server room, can instantly become a digital disaster. A comprehensive security at office plan must be integrated. Physical, digital, and human elements must work together in a single, cohesive strategy. A visitor management system helps bridge these gaps, connecting physical entry points with digital records and alerts to create a unified defense.
How Often Should We Update Our Security Protocols?
Security is not a "set it and forget it" task. Threats are constantly evolving. As a rule, conduct a formal review of your entire security plan at least once a year. However, you should perform an immediate review following any significant change, such as:
- Moving to a new office.
- Implementing a major new software system.
- Experiencing a security incident or a near miss.
Continuous reviews, penetration testing, and ongoing employee training are essential for resilience. Attackers relentlessly exploit known software vulnerabilities, underscoring the need for timely patching and protocol updates. A proactive approach is the only way to maintain a strong defense against future threats.
Ready to transform your front desk into a secure and efficient hub? VisitUs provides a modern visitor management system that gives you complete control and visibility over who is in your building. Strengthen your security, ensure compliance, and create a safer environment for your entire team. Learn more and see how VisitUs works.





